Changing the default RDP port¶
The process of changing the remote RDP access service port 3389(TCP) is described in the official Microsoft documentation Change the listening port for Remote Desktop on your computer
Applies to: Windows 10, Windows 8.1, Windows 8, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2008 R2
When connecting to the computer (a Windows or Windows Server client) via the remote desktop client, the remote desktop function on your computer will ‘hear’ the connection request via the defined listening port (tcp/3389 by default).
You can change the listening port on Windows computers by modifying the registry.
Important
If you use a firewall, be sure to set the firewall to allow the connection to the new port number. To do this, create a new rule for incoming traffic, specifying the TCP protocol and the port number that will be used for connection by RDP.
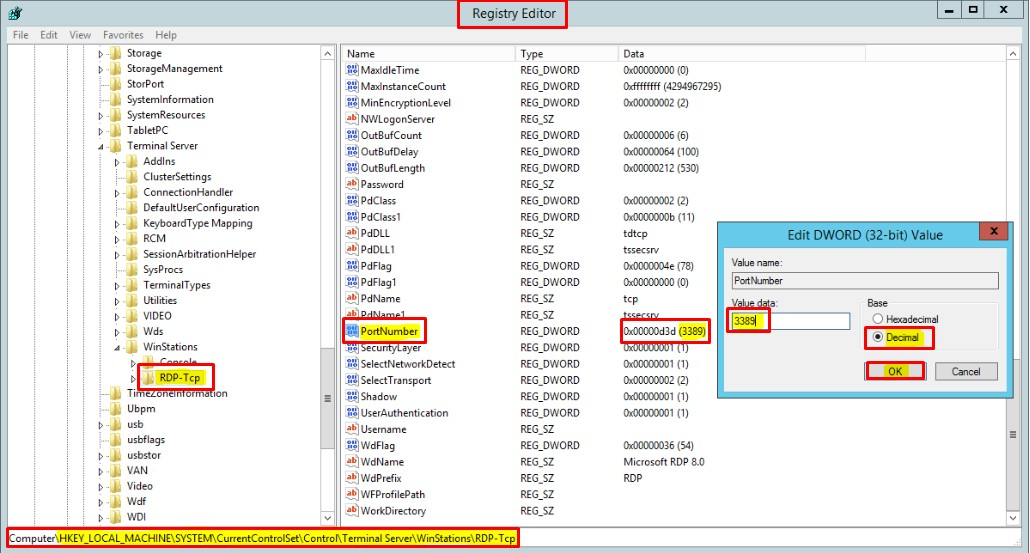
- Open the registry editor. (Enter ‘regedit’ in the search field.)
- Go to the following section of the registry:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp\PortNumber
- Press ‘Edit’ > ‘Change’, and then press ‘Decimal Number’.
- Enter the new port number and press the ‘OK’ button.
- Close the registry editor and restart the computer.
Next time you connect to this computer using the remote desktop connection, be sure to enter the new port.
Hint
To change the port quickly you can execute the command via the PowerShell or using the CMD command line with administrator rights. The following command will execute the same actions as those described above.
REG ADD "HKLM\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber /t REG_DWORD /d <new-port> /f
Example:
REG ADD "HKLM\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /v PortNumber /t REG_DWORD /d 5588 /f
where 5588 - is the new port that will be used for connecting by RDP.
Attention
After changing the service port, be sure to copy the changes into the firewall and also to the security group for the project.